Flashboot is a system built by Damien Miller and others as an adaptation of OpenBSD that's more suited for small flash-based hardware (like the like Soekris or Wrap machines). For most applications you don't have to compile it on you own, you just put the binary release on a flashcard and you're set (somewhat simplified).
Friday, December 28, 2007
OpenBSD "distribution" for embedded hardware
Posted by
cmihai
at
4:41 PM
0
comments
![]()
Labels: BSD, Open Source
Tuesday, December 25, 2007
Free Official Windows SteadyState - Rollback tool (like Deep Freeze)
Something cool for shared computers, Internet Cafes and such:
http://www.microsoft.com/windows/products/winfamily/sharedaccess/default.mspx
It's basically a free official DeepFreeze for Windows XP and Vista.
You can basically perform rollback an undo whole sessions.
Posted by
cmihai
at
2:42 AM
0
comments
![]()
Labels: Enterprise, Internet, Microsoft
Monday, December 24, 2007
Run ancient UNIX v5 on your Gameboy with gbaunix
Bored? Why not run UNIX 5th edition on your gameboy..
http://www.kernelthread.com/publications/gbaunix/
Double bored? Emulate the GBA :P.
Posted by
cmihai
at
11:24 PM
0
comments
![]()
Labels: BOFH, UNIX, Virtualization
Sunday, December 23, 2007
Free Veritas Cluster Server (VCS) Simulator
Veritas Cluster Server (VCS) is a High Availability (HA) cluster software for Linux, UNIX and Windows systems.
Symantec (they have bought Veritas) offers a freely available VCS emulator software that lets you train your skills :-).
You can also use the freely available documentation. Here is the Solaris Veritas Cluster Server (VCS) manual.
Of course, you could just grab the trial and run 2 Solaris (or Linux) virtual machines in VMware Server :-).
Posted by
cmihai
at
9:59 PM
5
comments
![]()
Labels: Clustering, Enterprise, Linux, Networking, UNIX, Virtualization
HP Calculator Emulators for the PC - your very own HP-48
HP-48 was a graphing calculator that uses Reverse Polish notation using RPL (Reverse Polish LISP). It's pretty the best calculator. Ever.
http://www.hpcalc.org/hp48/pc/emulators/
The HP calculators are fully programmable, and you can also download a LOT of applications for it. Even games :-).
Posted by
cmihai
at
5:37 PM
0
comments
![]()
Labels: Hardware, Software Development, Virtualization
Saturday, December 22, 2007
6000 CPU Linux Cluster in a single 20KW machine
"SiCortex 5832 is a 5-teraflop single-unit supercomputer."
Bet that got your attention.
"It uses low-power, custom 64-bit MIPS-processor packages, which are basically entire computers on a single chip. 5832 processor cores and 8TB of RAM in one chassis, which draws less than 20 kilowatts of power."
"The SiCortex systems are completely open source, even down to the microcode."
They even say it runs a modified version of *cough* Gentoo Linux and the (now Sun) Lustre Filesystem.
SiCortex also offers a 72 CPU desktop machine that's as big.. well, as a desktop machine :-).
Say hell yes to Desktop HPC:
Read more about their Kautz digraph based fabric and implementation here:
http://www.sicortex.com/products/white_papers
Posted by
cmihai
at
8:18 PM
1 comments
![]()
Labels: Clustering, HPC, Linux, Mainframe, Open Source, Sun
mssigstub.exe - random directories
Ever notice a random looking directory on your drives? And some files like mssigstub.exe or sigstub.exe inside, signed "Microsoft Code Signing PCA", described as "Microsoft Malware Protection Signature Update Stub"?
Well, I have, and it's Windows Defender, using the disk with most free space available to store TEMP files. So much for $TEMP. Safe to delete btw.
Posted by
cmihai
at
12:41 AM
0
comments
![]()
Labels: Microsoft
Friday, December 21, 2007
A brief look at ClamAV security - Open Source Antivirus
A brief (over)look at ClamAV security and performance. Comparing Open Source Antivirus products with commercial products. AV-Test is an anti-virus research project at the Institute of Technical and Business Information Systems at the Otto-von-Guericke University Magdeburg (Germany). They measured the detection times for six of the malware programs released last week utilizing the MS05-039 Plug and Play vulnerability under 36 different anti-virus products. Eleven of the products were able to detect one or more of the attacks proactively, without any special pattern update to identify it specifically. Here are the numbers for each of the eleven:
I've been looking into signature based open source security products lately, namely Antivirus software (for SMTP E-Mail gateways or File Servers or anything that would be used as a distribution point for example as well as for Desktop systems).
I've had a pretty good look at ClamAV and other ClamAV based products (ClamWin or Spyware Terminator which include the ClamAV Engine) and found them rather weak, both from a security point of view (vulnerabilities) and in terms of detection rates, as well as performance (speed) and usability (interface, features, etc).
Clam AntiVirus (ClamAV) is an open source (GPL) anti-virus toolkit for UNIX (also ported to Windows, and used by GUI products such as ClamWin) designed especially for e-mail scanning on mail gateways. It provides a number of utilities including a flexible and scalable multi-threaded daemon, a command line scanner and advanced tool for automatic database updates. The core of the package is an anti-virus engine available in a form of shared library.
I. Security track record - a look at common vulnerabilities
So let's take a look at ClamAV's security track record. A simple look on Secunia at the vulnerability summary reveals a stunning 25 security advisories (1 unpattched), 31 % of which lead to System Access and 91 % are exploitable from remote. 40 % of vulnerabilities are "Highly Critical". I realize that some of these are in 3rd party plugins and compression tools and such, but when an attacker just sends a specially crafted archive via E-mail or whatever means, and manages to buffer overflow and gain system access when ClamAV scans it, that's when you need to look at other products. There are ways to mitigate it, with permissions, limited users, chroots, jails and such, but still...
So let's compare that with another security product, Avira Antivir, basically multi-platform Antivirus software (also has a free version for non-commercial usage). We can see only 2 security vulnerabilities reported, both local and privilege escalation (Windows only too).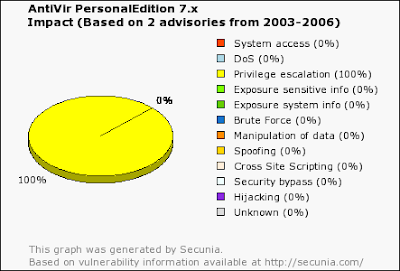
Vulnerabilities range from Denial of Service: "A NULL-pointer dereference error exists within the "cli_scanrtf()" function in libclamav/rtf.c. This can potentially be exploited to crash ClamAV via a specially crafted RTF file." to Buffer Overflow and System Access: "An integer overflow error in rebuildpe.c when rebuilding PE files after unpacking can be exploited to cause a heap-based buffer overflow via a specially crafted executable. Successful exploitation of this vulnerability may allow execution of arbitrary code."
II. Vulnerability assessment tools - Static Code Analsys
What about a source code audit of ClamAV? Well, I don't really have the time for that, but I did parse it through Flawfinder, RATS and other Static Code Analysis tools looking for simple lexical "bad practices" and functions (strings functions for example) that may overflow buffers and so on.
So, I download the source code for the latest stable release: ClamAV 0.91.2 (signature) and stumble across a ton of bad programming practices. While most of the time, they mean nothing (as they aren't really vulnerabilities or even exploitable, they are usually where most errors occur, and, as such, should be avoided). We basically have hundreds of such occurrences (537 marked as High and 83 marked as Medium by RATS), so I'm just going to paste a few interesting examples here:
..\clamav-0.91.2/clamav-milter/clamav-milter.c:266: High: fixed size local buffer
Extra care should be taken to ensure that character arrays that are allocated on the stack are used safely. They are prime targets for buffer overflow attacks.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:859: High: getopt_long
Truncate all input strings to a reasonable length before passing them to this function
..\clamav-0.91.2/shared/getopt.c:961: High: fprintf
Check to be sure that the non-constant format string passed as argument 2 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle.
..\clamav-0.91.2/sigtool/vba.c:1127: High: sprintf
Check to be sure that the format string passed as argument 2 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle. Additionally, the format string could contain `%s' without precision that could result in a buffer overflow.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:1205: High: popen
Argument 1 to this function call should be checked to ensure that it does not come from an untrusted source without first verifying that it contains nothing dangerous.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:1404: High: getenv
Environment variables are highly untrustable input. They may be of any length, and contain any data. Do not make any assumptions regarding content or length. If at all possible avoid using them, and if it is necessary, sanitize them and truncate them to a reasonable length.
..\clamav-0.91.2/shared/output.c:159: High: umask
umask() can easily be used to create files with unsafe priviledges. It should be set to restrictive values.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:1585: High: gethostbyname
DNS results can easily be forged by an attacker (or arbitrarily set to large values, etc), and should not be trusted.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:1703: High: strcpy
Check to be sure that argument 2 passed to this function call will not copy more data than can be handled, resulting in a buffer overflow.
..\clamav-0.91.2/shared/misc.c:132: High: printf
Check to be sure that the non-constant format string passed as argument 1 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle.
..\clamav-0.91.2/shared/output.c:235: High: syslog
Truncate all input strings to a reasonable length before passing them to this function
..\clamav-0.91.2/freshclam/manager.c:1307: High: system
Argument 1 to this function call should be checked to ensure that it does not come from an untrusted source without first verifying that it contains nothing dangerous.
..\clamav-0.91.2/sigtool/sigtool.c:815: High: strcat
Check to be sure that argument 2 passed to this function call will not copy more data than can be handled, resulting in a buffer overflow.
..\clamav-0.91.2/libclamav/hashtab.c:408: High: sscanf
Check to be sure that the format string passed as argument 2 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle. Additionally, the format string could contain `%s' without precision that could result in a buffer overflow.
..\clamav-0.91.2/shared/options.c:194: High: strncat
Consider using strlcat() instead.
..\clamav-0.91.2/shared/options.c:194: High: strncat
Check to be sure that argument 1 passed to this function call will not copy more data than can be handled, resulting in a buffer overflow.
..\clamav-0.91.2/shared/getopt.c:983: High: getopt
Truncate all input strings to a reasonable length before passing them to this function
..\clamav-0.91.2/shared/output.c:212: High: vfprintf
Check to be sure that the non-constant format string passed as argument 2 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle.
..\clamav-0.91.2/sigtool/sigtool.c:609: High: scanf
Check to be sure that the format string passed as argument 2 to this function call does not come from an untrusted source that could have added formatting characters that the code is not prepared to handle. Additionally, the format string could contain `%s' without precision that could result in a buffer overflow.
..\clamav-0.91.2/test/pe/debugpe.c:165: Medium: signal
When setting signal handlers, do not use the same function to handle multiple signals. There exists the possibility a race condition will result if 2 or more different signals are sent to the process at nearly the same time. Also, when writing signal handlers, it is best to do as little as possible in them. The best strategy is to use the signal handler to set a flag, that another part of the program tests and performs the appropriate action(s) when it is set.
See also: http://razor.bindview.com/publish/papers/signals.txt
..\clamav-0.91.2/libclamav/mbox.c:4659: Medium: getc
Check buffer boundaries if calling this function in a loop and make sure you are not in danger of writing past the allocated space.
..\clamav-0.91.2/sigtool/sigtool.c:172: Medium: read
Check buffer boundaries if calling this function in a loop and make sure you are not in danger of writing past the allocated space.
..\clamav-0.91.2/clamav-milter/clamav-milter.c:4260: Medium: stat
A potential TOCTOU (Time Of Check, Time Of Use) vulnerability exists. This is the first line where a check has occured. The following line(s) contain uses that may match up with this check: 4269 (open)
..\clamav-0.91.2/sigtool/vba.c:1063: Medium: realloc
Don't use on memory intended to be secure, because the old structure will not be zeroed out.
..\clamav-0.91.2/libclamav/lockdb.c:246: Medium: SetSecurityDescriptorDacl
If the third argument, pDacl, is NULL there is no protection from attack. As an example, an attacker could set a Deny All to Everyone ACE on such an object.
..\clamav-0.91.2/libclamav/msexpand.c:130: Medium: fgetc
Check buffer boundaries if calling this function in a loop and make sure you are not in danger of writing past the allocated space.
..\clamav-0.91.2/libclamav/others.c:433: Medium: srand
Standard random number generators should not be used to generate randomness used for security reasons. For security sensitive randomness a crytographic randomness generator that provides sufficient entropy should be used.
..\clamav-0.91.2/libclamav/others.c:697: Medium: lstat
A potential TOCTOU (Time Of Check, Time Of Use) vulnerability exists. This is
the first line where a check has occured.
The following line(s) contain uses that may match up with this check:
699 (rmdir), 715 (unlink)
..\clamav-0.91.2/contrib/Windows/Projects/clamAV/libclamav/regex.c:70: Medium: realloc
Don't use on memory intended to be secure, because the old structure will not be zeroed out.
You should keep in mind that ClamAV also relies on 3rd party libraries and tools, and it's security also depends on those. Again, I remind you that these aren't actual vulnerabilities, just bad practices that MAY lead to such vulnerabilities. You would need to look at the code and employ various testing tools to find them.
The authors of ClamAV should really solve these problems like OpenBSD developers do, even if it is something as simple as replacing strncat() with strlcat() - functions designed to be safer, more consistent, and less error-prone (this would be an issue on other platforms though, so it's not as simple as that).
III. Detection rates
So, here are some tests made by various research projects:
BitDefender 6 of 6 Fortinet 6 of 6 Nod32 5 of 6 eSafe 3 of 6 F-Prot 3 of 6 Panda 3 of 6 QuickHeal 3 of 6 McAfee 2 of 6 Norman 2 of 6 AntiVir 1 of 6 ClamAV 1 of 6
AV Comparatives did a test on various other Antivirus products not in their current testing process, including the ClamAV based ClamWin. Here are the results:
http://www.av-comparatives.org/seiten/ergebnisse/2ndgrouptest.pdf
This test also places ClamAV among the last in terms of detection rates:
http://www.sunbelt-software.com/ihs/alex/malwarereportjun3007.pdf
ClamAV also scores a 17 % (sig: 99% / heur: 1%) in retrospective Antivirus Performance Statistics, which also placed it among the last.
At VirusPool Tested Products ClamAV scores:
Number of descriptions in the database: 31928 out of 45159 live samples ( 70.7 %)
Number of 'in the wild' descriptions in the database: 25 out of 30 live samples ( 83.3 %)
(not very good, but not all that bad)
IV. Signature Updates:
How often is the clamav-virusdb updates? According to the FAQ, multiple times a week, and the response should be rather prompt. Anyway, to get an idea on that, take a look at http://lurker.clamav.net/list/clamav-virusdb.html
Conclusion:
I definitely need to investigate this further, but so far I find ClamAV to be highly overrated, simply based on the fact it is "part of the open source movement". It lacks a real time scanner (that's fair seeing how it was designed for mail gateways though), it has a horrible security track record, poor detection rates and dreadful performance. I somewhat doubt that it would last long as a commercial product. Still, it is available on multiple platforms, and the cost is just about right :-).
Things aren't all bad though (and I may have been to rash and only brushed the surface here). ClamAV is a free product (open source even), and it does leave a lot of room an opportunity to evolve. I just don't see this happening without powerful commercial backing. If you plan on using it though, make sure you've got at least another product scanning your emails :-).
Other links:
http://www.av-comparatives.org/
http://www.virustotal.com/
Posted by
cmihai
at
8:03 PM
0
comments
![]()
Labels: Debugging, Digital Forensics, Internet, Linux, Security, UNIX, Vulnerability Assessment
Johnny Lee's back with more Wii hacks - Head Tracking
Virtual Reality, Cheap! Johnny is back with more Wii hacks. This time, he uses the Wii infrared camera (Wii Remote) to perform head tracking (using 2 Infrared LEDs or the Nintendo Sensor Bar). Basically, this allows him to use the data for positioning the viewer's head in space (by solving the triangle) and move the displayed data around to emulate a 3D display.
He makes the source code to his applications fully available, so if you feel like using a 3D display, an air keyboard or a virtual chalkboard, check his projects:
http://www.cs.cmu.edu/~johnny/projects/wii/
Posted by
cmihai
at
7:41 PM
0
comments
![]()
Labels: BOFH
OpenBSD automated / unattended installation - Yaifo
Don't have remote servers with KVM? Well, this will help:
Yaifo has been updated for OpenBSD 4.2 and is now actively maintained by Mike Erdely. You can download it here:
http://erdelynet.com/category/tech/yaifo/
It's basically a modified installer with ssh support, RAID support and all that. You can basically do remote, scripted, unattended OpenBSD installations, etc.
Posted by
cmihai
at
6:37 PM
0
comments
![]()
Labels: BSD, Open Source, Scripting
Windows Automated Installation Kit - Unattended Vista installation
Windows Automated Installation Kit (WAIK) lets you install, customize, and deploy the Microsoft Windows Vista. It lets you perform unattended installations of Windows, create Windows Images with ImageX and create Windows PE images. This is basically like vLite (Windows Vista Configuration Tool), but, well.. official :-).
Download the Windows Automated Installation Kit (WAIK) User's Guide for Windows Vista here.
Download the Windows Automated Installation Kit (AIK) here.
Deploying Windows Vista TechNet.
You may also want to look at Business Desktop Deployment 2007 for Windows Vista and Office 2007 deployment scripting and tools.
Download Business Desktop Deployment 2007 here.
More tools and ways for Enterprise mass Windows deployment here.
For UNIX deployment tools and procedures go here.
Posted by
cmihai
at
4:35 PM
0
comments
![]()
Labels: Enterprise, Microsoft, UNIX
Thursday, December 20, 2007
Uninstalling Blastwave (or any other package group) with a bit of Shell Scripting on Solaris.
Let's say we've installed a bunch of Solaris packages from Blastwave or another source and want to remove them all without going through the boring process of answering all those questions:
$ pkginfo | grep CSW
system CSWcommon common - common files and dirs for CSW packages
application CSWexpat expat - XML Parser Toolkit
system CSWggettext ggettext - GNU gettext
application CSWglib2 glib2 - the low-level core library for GTK+ and GNOME
system CSWiconv libiconv - GNU iconv library
application CSWmc mc - GNU Midnight Commander
system CSWpkgget pkg_get - CSW version of automated package download tool
system CSWslang slang - library primarily to provide an alternative to libcurses
system CSWsunmath libsunmath - Sun maths library
Well, nothing simpler:
# yes | pkgrm $(pkginfo | grep CSW | awk '{ print $2 }' | xargs)
The following package is currently installed:
CSWcommon common - common files and dirs for CSW packages
(i386) 1.4.5
Do you want to remove this package? [y,n,?,q]
## Removing installed package instance
## Verifying packagedependencies in global zone
[.....]
Removal ofwas successful.
# pkginfo | grep CSW
#
Since Blastwave installs by default in /opt/csw, you can probably remove that too if you don't have settings you plan on keeping:
# rm -rf /opt/cswEnjoy :-).
Posted by
cmihai
at
4:42 PM
1 comments
![]()
Labels: Open Source, Scripting, Solaris, Sun
Killing defunct (zombie) processes on Solaris - preap and orphan processes with init(1M)
A defunct (or zombie) process is one whose exit status has yet to be reaped by its parent. So when a process shows as "defunct" in ps, you need to reap it. Here's how:
preap(1) - force a defunct process to be reaped by its parent
Syntax: /usr/bin/preap PIDSo, to get rid of all zombies on our system, all we have to do is script this to real all process marked as defunct:
/usr/bin/preap $(ps -ef | grep defunct | awk '{ print $2 }' | xargs)So, what's an orphan process then? If the parent of a defunct process happens to exit, it becomes an orphan, and is asigned PID 1 as a parent - see init(1M).
Read more on zombies, defunct processes, orphans, preap and init here.
Posted by
cmihai
at
4:32 PM
1 comments
![]()
Core Java - 8th edition
The 8th edition of Core Java is out, one of the best books on practical Java programming. The source code is freely available for download.
http://horstmann.com/corejava.html
Posted by
cmihai
at
1:04 PM
0
comments
![]()
Labels: Software Development
Wednesday, December 19, 2007
NetBSD 4.0 Released, 54 platforms supported.
NetBSD 4.0 Release announcement.
Major changes in NetBSD 4.0:
- Xen 3
- Blueetooth Support
- iSCSI support
- CARP - The (OpenBSD) Common Address Redundancy Protocol
- mprotect(2) to enforce OpenBSD's W^X policies
- Kernel Authorization Framework
- Veriexec file integrity subsystem
http://www.netbsd.org/mirrors/
Also, consider donating to the NetBSD project:
http://www.netbsd.org/donations/
Posted by
cmihai
at
9:10 PM
0
comments
![]()
Labels: BSD, Open Source
Tuesday, December 18, 2007
Gigabyte i-RAM memory disk - acts like regular SATA disk
iRAM is a RAMDISK that acts like a regular SATA drive, but uses DDR memory modules(4 battery backed 184-pin DIMM slots that accept any DDR DIMM and support up to 4GB unbuffered / non-ECC memory).
http://techreport.com/articles.x/9312
Some cool usage: Using more iRAM drives in a RAID-0 :-).
http://kiti.main.jp/Report/Waller/Waller1.htm
http://kiti.main.jp/Report/Waller/Waller2.htm
Posted by
cmihai
at
6:51 PM
0
comments
![]()
Mondo Backup - GPL Bare Metal Recovery Solution
Here's an interesting alternative to using CloneZilla and the likes for Bare Metal Recovery:
Mondo Rescue is a free (GPL) powerful disaster recovery suite for Linux (i386, x86_64, ia64) and FreeBSD (i386). It's packaged for multiple distributions (RedHat, RHEL, SuSE, SLES, Mandriva, Debian, Gentoo). It's basically the Linux equivalent of the powerful AIX mkcd / mkdvd.
It supports backups to tapes, disks, network and CD/DVD. It also supports multiple filesystems (ext2, ext3, JFS, XFS, ResierFS, VFAT and even NTFS), LVM, software and hardware Raid.
Example of using Mondo Rescue:
Generate a bootable DVD that also backs up /etc and can recover files running mondorestore:
# mondoarchive -OVr -d /dev/dvd -9 -I /etc -gFAnother interesting tool worth checking out is System Imager (automates Linux installs).
Posted by
cmihai
at
5:22 PM
0
comments
![]()
Labels: Backup, Enterprise, Linux, Open Source
Monday, December 17, 2007
Why I hate Gnome...
I have been using GNOME for over 7 years now, and feel that with every release it gets more unstable, buggy and bloated. Good features get removed or reimplemented in some horribly broken form. Or they just mess around with sane default settings (see Always Open in Browser windows to Windows 95 style open a new window for each browser). Sometimes they hide the icons, the trash can, the delay settings... and they so love to complicate the configuration files. But now....
It looks like GNOME is desperately trying to become the new "Microsoft BOB":
Bug 324253 – "New document" and "Open terminal" non active by default in context menu
- "Open terminal" is frustrating (and scary) for users not knowing what to do with a terminal, the vast majority of GNOME users nowadays. If anybody needs to open a terminal there is an easy way to do so through Applications. If really needed, the user could activate this preference from Preferences.
Yes people, that is why the right click - open terminal shortcut was REMOVED from Gnome 2.14 and later. It's a BUG since it SCARES away users. Boooo.. and now you need to install a "plugin" like nautilus-open-terminal. WTF. Yes, all users must be retarded, let's remove a useful feature...
Linus Torvalds had some things to say about Gnome too:
"This 'users are idiots, and are confused by functionality' mentality of Gnome is a disease. If you think your users are idiots, only idiots will use it. I don't use Gnome, because in striving to be simple, it has long since reached the point where it simply doesn't do what I need it to do."
Where Gnome aims to be in 5 years:
// Sorry for the rant, but I just had to get his off my chest... I miss Sawfish :-(.
Posted by
cmihai
at
11:33 PM
6
comments
![]()
Labels: BOFH, Internet, Open Source
OpenSolaris ATI Direct Rendering Infrastructure and 3D drivers
The Direct Rendering Infrastructure(a.k.a.DRI) is a framework for allowing direct access to graphics hardware under the X Window System in a safe and efficient manner. It includes changes to the X server, to several client libraries, and to the kernel. The first major use for the DRI is to create fast OpenGL implementations.
This project is targeted to port open-sourced DRI framework to Solaris, and provide 3D acceleration for Solaris x86. Meanwhile we would work with hardware vendors to enhance the 3D performance.
http://opensolaris.org/os/project/dri/
Commercial NVIDIA drivers are already included in OpenSolaris (and Solaris) distributions and are also available from nvidia.com.
Posted by
cmihai
at
9:47 PM
0
comments
![]()
Labels: Open Source, Solaris, Sun
OpenBSD and USB audio cards
If you have a USB audio card - uaudio(4) you must configure OpenBSD to use the proper sound device:
$ tail -f /var/log/messages
Plug in your USB audio card...
Use usbdevs(8) and dmesg(8) to figure out what audio devices it uses...
Configure /dev/audio, /dev/audioctl, /dev/mixer to point to /dev/audio1 or whatever dmesg reports as your new audio card and check if everything is OK;
$ ls -l /dev/audio* /dev/audioctl* /dev/mixer* /dev/sound* && audioctl -a && mixerctl -a"
Test your sound:
Enjoy.
"cat /dev/urandom > /dev/audio"
Posted by
cmihai
at
7:01 PM
1 comments
![]()
Labels: BSD
Unlocking MacOS FileVault Whitepapers, Video and Audio
FileVault is an encryption system found in Apple's Mac OS X v10.3 and later. It has quite a history of being vulnerable to watermarking attacks, not encrypting the swap file by default (although that option has been added later) so that the keys could be carved out of the page file, etc...
A few resources on FileVault (AKA VileFault) shortcomings:
- Unlocking FileVault Talk at 23c3 (video)
- Unlocking FileVault Talk at 23c3 (audio)
- Unlocking FileVault Whitepaper
- An Unencrypted Look at FileVault
Posted by
cmihai
at
5:52 PM
0
comments
![]()
Labels: Cryptology, Digital Forensics, Security, UNIX
Recovering data from the EXT2 Filesystem
EXT2 Undelete: A pretty good tutorial for recovering data from ext2 filesystems:
http://fedora.linuxsir.org/doc/ext2undelete/Ext2fs-Undeletion.html
See also:
- Filesystem tools: Data Recovery and Data Carving (you can use Foremost, Scalpel or FTimes to carve out a LOT of data from a drive).
- The Second Extended File System - Internal Layout
Posted by
cmihai
at
10:33 AM
4
comments
![]()
Labels: Digital Forensics, Linux, Open Source
Sunday, December 16, 2007
Debian Etch AMD64 NVIDIA install one-liner
Add contrib and non-free repositories to sources.list:
cmihai@db:~$ cat /etc/apt/sources.list
deb http://ftp.lug.ro/debian/ etch main contrib non-free
deb-src http://ftp.lug.ro/debian/ etch main contrib non-free
deb http://ftp.lug.ro/debian-security etch/updates main contrib non-free
deb-src http://ftp.lug.ro/debian-security etch/updates main contrib n
Install the packages and configure X (nvidia-xconfig).
$ sudo aptitude install nvidia-kernel-2.6-`uname -r | sed 's,.*-,,g'` nvidia-settings nvidia-glx nvidia-xconfig nvidia-glx-ia32 && nvidia-xconfig
Posted by
cmihai
at
8:05 PM
0
comments
![]()
PCA - Analyze, download and install patches for Solaris
Trouble with Sun Solaris Patching? Sick of all those tools (smpatch, getsolpatch, Sun Update Connection, Patch Manager PatchPro, PatchCheck, PatchDiag, patchadd) that get dropped or are poorly maintained, broken, etc? Well, here's yet another tool to "fix'em all".
"Patch Check Advanced (pca) generates lists of installed and missing patches for Sun Solaris systems and optionally downloads patches. It resolves dependencies between patches and installs them in correct order. It can be the only tool you ever need for patch management on a single machine or a complete network. Just one perl script, it doesn't need compilation nor installation, and it doesn't need root permissions to run. It works on all versions of Solaris, both SPARC and x86."
Seriously though, PCA rocks ;-).
Posted by
cmihai
at
12:41 AM
0
comments
![]()
Labels: Enterprise, Open Source, Scripting, Solaris, Sun
Saturday, December 15, 2007
Windows Server 2008 RC1 Enterprise with Hyper-V Beta x64 available for Download
Windows Server 2008 RC1 Enterprise is now available with a beta version of Windows Server Hyper-V, a key feature of Windows Server 2008 that will be included in Standard, Enterprise, and Datacenter x64 editions.
An earlier Customer Technology Preview (CTP) of Hyper-V, is also available for download with Windows Server 2008 RC1 Standard, Enterprise, and Datacenter x64 editions.
This version of Hyper-V includes high availability and quick migration features, and is installable under the reduced (no GUIs version) "Core Server" version of Windows Server 2008. It also supports Windows and Linux guests, and snapshots.
Posted by
cmihai
at
12:00 PM
0
comments
![]()
Labels: Enterprise, Microsoft, Virtualization
Friday, December 14, 2007
Sun Secure Global Desktop (Tarantella) - Enterprise Remote Desktop
Sun Secure Global Desktop (aka Tarantella) provides secure access (SSL - HTTPS) to centralized UNIX, Windows, Mainframe and Midrange applications from a wide range of popular client devices, including Microsoft Windows PCs, Solaris OS Workstations, thin clients and mobile devices.
Tarantella is a competitor to Terminal Services from Microsoft and Citrix software, but it's much more interesting (It's got Windows and Citrix connectors, Thin Client stuff, etc). It's basically like GNU Screen (you can resume sessions and easily migrate between machines), but for X and via your web browser :-).
If you want to try this baby out, you'll need a Solaris or Linux machine. Download Tarantella from http://www.sun.com/software/products/sgd/get.jsp
The fun part is, with Solaris 10 you can simply install Tarantella in a Zone (Solaris Container).
Before you install SSGD you must define (and secure) the users:
- The user names must be "ttaserv" and "ttasys".
- Both must have their primary group set to "ttaserv".
- You can use any UIDs and GID you want.
- The ttaserv/ttasys users must have a valid shell, for example /bin/sh.
- We recommend that you lock the ttaserv/ttasys user accounts (passwd -l).
- The users must have a valid home directory too, so if you're using /export/home (/home is the home of the automounter) make sure you do it right.
One quick way to do that is:
# groupadd ttaserv
# useradd -g ttaserv -s /bin/sh -d /export/home/ttaserv ttaserv
# mkdir /export/home/ttaserv
# chown ttaserv:ttaserv /export/home/ttaserv
# passwd -l ttaserv
# useradd -g ttaserv -s /bin/sh -d /export/home/ttasys ttasys
# mkdir /export/home/ttasys
# chown ttasys:ttaserv /export/home/ttasys
# passwd -l ttasys
Check if the user accounts are setup correctly:
# su ttaserv -c "/usr/bin/id -a"
uid=101(ttaserv) gid=100(ttaserv) groups=100(ttaserv)
# su ttasys -c "/usr/bin/id -a"
uid=102(ttasys) gid=100(ttaserv) groups=100(ttaserv)
Install the SSGD package:
# cp tta-4.40-907.sol-x86.pkg.gz /tmp; cd /tmp; gunzip tta-4.40-907.sol-x86.pkg.gzTo complete the installation and select options (port, etc), run /opt/tarantella/bin/tarantella start - configuration may take a while...
# pkgadd -d /tmp/tta-4.40-907.sol-x86.pkg
Once SSGD is installed (I chose installing it /opt by default) you can use:
# /opt/tarantella/bin/tarantella statusThe security start requires a valid security license and a SSL certificate (you can create a self signed certificate using OpenSSL then import with SSGD).
# /opt/tarantella/bin/tarantella start
# /opt/tarantella/bin/tarantella stop
# /opt/tarantella/bin/tarantella security start
To add license keys, type:
/opt/tarantella/bin/tarantella license addOnce SSGD is installed and started, just navigate any Java enabled browser to http://yoursite.yourdomain:selectedport and you're good to go :-). Use "Administrator" and the root password to login. (Use regular system accounts for non-administrative purposes. Oh, and secure SSGD by using Zones).
Be sure to check the documentation on docs.sun.com:
http://docs.sun.com/app/docs/coll/SSGD_4.2
Posted by
cmihai
at
11:49 AM
0
comments
![]()
Labels: Enterprise, Networking, Security, Solaris, Sun
QNX Releases Source Code for New Networking Stack based on NetBSD
New QNX Neutrino Real Time Operating System Network Stack source code available, based on NetBSD code.
"Based largely upon the NetBSD4 code base, the stack includes a number of new features that address security, enhance speed, and aid in code portability."
Article on CNN Money
Posted by
cmihai
at
11:37 AM
1 comments
![]()
Labels: BSD, Open Source, QNX
Wednesday, December 12, 2007
A few more tools to unerase files
A few free tools to restore deleted files:
- Undelete Plus works under Win 95/98/Me/NT/2000/XP/2003/Vista operating systems. The program supports all Windows file systems for hard and floppy drives including FAT12/16/32,NTFS/NTFS5 and image recovery from CompactFlash, SmartMedia, MultiMedia and Secure Digital cards.
- Recuva (pronounced "recover") is a freeware Windows utility to restore files that have been accidentally deleted from your computer.
- Restoration - free undelete tool for Windows.
- NTFS Undelete - free undelete tool for Windows.
- R-LINUX is a free file recovery utility for the Ext2FS partitions used in the Linux OS and several Unix. Host OS: Win9x/ME/NT/2000/XP/2003. Recovered data can be written to any disk visible by the host OS. R-Linux also can create DISK IMAGES that can be later processed by more powerful R-Studio. more about Data Recovery for Linux
- Ultimate Data Recovery - data recovery tool.
Posted by
cmihai
at
9:32 PM
1 comments
![]()
Labels: Digital Forensics, Linux, Microsoft
Cool April RFCs - RFC 1149 - IP datagrams on avian carriers - Pigeon and OCR Implementation
A couple of cool April 1st RFC's:
RFC 1149:Standard for the transmission of IP datagrams on avian carriers
RFC 2549: IP over Avian Carriers with Quality of Service
Of course someone "wrote" an implementation...
http://blug.linux.no/rfc1149/index.html
Pictures from the worlds first RFC 1149 implementation. (IP datagrams printed, transmitted via pigeon messages, scanned, OCR-ed and re-assembled).
Karl Magnus with a test packet:
PS: the bloke in the Red Hat [SIC] is Alan Cox, Linux kernel developer.
Posted by
cmihai
at
3:19 PM
1 comments
![]()
Labels: BOFH, Internet, Networking
Cool new Winamp Skin - Bento - and Winamp 5.5; Slayradio
Winamp 5.5 is out with a pretty cool new skin.
Oh, and did I mention SlayRadio rocks (Commodore 64 and Amiga remixes)?
Posted by
cmihai
at
2:45 PM
0
comments
![]()
Labels: Microsoft
Office 2007 SP1, Windows security updates; IE vulnerabilities
Fresh updates for Windows, including Office 2007 SP1 and some vital security updates including some IE vulnerability fixes. Better start those WSUS deployments for distributed update servers if you don't have one already :-).
See also:
Internet Explorer Multiple Code Execution Vulnerabilities - Extremely critical, from remote, system access. This vulnerability is reportedly being actively exploited. - http://secunia.com/advisories/28036/
https://www.microsoft.com/technet/security/bulletin/ms07-dec.mspx
http://isc.sans.org/diary.html?storyid=3735
Posted by
cmihai
at
12:13 PM
0
comments
![]()
Tuesday, December 11, 2007
PersonalAlpha - Alpha CPU Emulator lets you run OpenVMS or Tru64 UNIX on your PC
I already told you about SIMH, the VAX emulator, now it's time to look at a working Alpha emulator (there is another one I know of that works, but it's rather expensive and intended for development purposes). This means you can run OpenVMS or Tru64 UNIX right at home, on your PC :-).
PersonalAlpha is a Alpha emulator that can run OpenVMS or Tru64 right on your i386 desktop machine.
You can use 128 MB of emulated Alpha memory, 1 Ethernet adapter, VT-terminal emulation and 4 disks.
Minimum requirements: A Windows machine, 1 GHz CPU, 1 GB of memory(512 MB will run with performance penalty), 1 Ethernet adapter and 4 GB of free disk space.
Now all you need to do is join the DECUS society (or Encompassus) and get yourself that free OpenVMS hobbyist kit and you're good to go :-).
Also, check out Virtutech Simics.
Various links and resources to other Alpha emulators / simulators /whatever:
http://www.simplescalar.com/
http://www.yuba.is.uec.ac.jp/~kis/SimCore/functional.htm
http://www.cs.ucsd.edu/users/tullsen/smtsim.html
https://systems.cs.colorado.edu/DistributedSoftware/Aint/
http://www.encompasserve.org/DECUServe/DECnotes/VMS/3411.1.HTML
https://systems.cs.colorado.edu/DistributedSoftware/Aint/
Posted by
cmihai
at
11:21 PM
4
comments
![]()
Labels: Enterprise, OpenVMS, UNIX, Virtualization
Monday, December 10, 2007
Xenix - a blast from the past - Looking back at Microsoft UNIX
Xenix was Microsoft's version of UNIX, licensed from AT&T back in the late 70s, then later acquired by the Santa Cruz Operation (SCO) and distributed as SCO UNIX. Microsoft did not sell Xenix directly to end-users, but instead licensed it to OEMs.
Xenix was originally based AT&T UNIX System III, but also incorporated elements from BSD. Version 2.0 was based on UNIX System V, and later ported to 32bit / i386, and also introduced TCP/IP and SCSI support.
Trusted Information systems also developed a Trusted Xenix variant, using the Bell-LaPadula model of multilevel security and achieved a NSA B2 rating (TCSEC) - the second highest rating ever achieved by an evaluated operating system.
Overall, it was a pretty complete UNIX system (later versions got as large as 96 5.25" floppy disks) and came with The X Window System, ed, vi, sh, csh, vsh, uucp, terminfo, mapchan and so on.
Good news is, you can run it yourself. There's at least 3 ways to run Xenix:
I. i386 Xenix
- Track down a 386 version... my floppies are all dead X-D
- Install using qemu
- Get the Xenix floppy images from http://www.catcorner.org/Tandy/ - This is a complete Xenix install for the Tandy 6000 series.
- Get a Tandy 6000 or write an emulator (none exists from what I've seen).
- Get a copy of Xenix for LISA: http://memo5.dyndns.org/Sites/Lisa/softs/othersofts.html - it took me a while to track this one down.
- Get a LISA Emulator: http://lisa.sunder.net - LisaEM is an Open Source multiplatform LISA Emulator.
- Enjoy!

Here's some Xenix documentation to get you started: http://www.tenox.tc/docs/
- Apple Lisa XENIX Programmers Guide
- Apple Lisa XENIX Programmers Reference
- IBM XENIX C Compiler Reference
- IBM XENIX Command Reference
- IBM XENIX Programmers Guide To Library Functions
- Microsoft Multiplan for the XENIX OS
- Microsoft XENIX 286 Press Release
- Microsoft XENIX 3.0 Release Summary
- Microsoft XENIX OEM Directory
- Microsoft XENIX Programmers Manual
- Tandy Xenix Customizing Scripsit 16
- Tandy Xenix Introducing Your Tandy 6000
- Tandy The System Administrators Guide To Xenix
- Tandy Xenix The Users Guide To Xenix
- Tandy Using Xenix 3.2.0
Posted by
cmihai
at
10:56 PM
5
comments
![]()
Turn a Wii into a whiteboard or tracking system
Now this is cool:
"Using an LED array and some reflective tape, you can use the infrared camera in the Wii remote to track objects, like your fingers, in 2D space."
"Since the Wiimote can track sources of infrared (IR) light, you can track pens that have an IR led in the tip. By pointing a wiimote at a projection screen or LCD display, you can create very low-cost interactive whiteboards or tablet displays. Since the Wiimote can track upto 4 points, multiple pens can be used."
http://www.cs.cmu.edu/~johnny/projects/wii/
Posted by
cmihai
at
10:38 AM
0
comments
![]()
Labels: BOFH
Sunday, December 09, 2007
Repair MBR in Windows using mbrfix, fixmbr, bootrec, testdisk, dd and gag
Accidentally rewritten your MBR (or even the partition table) and can't find your old Win9x friend, "fdisk /mbr"? Well, here's a couple of ways on how to fix it:
- Fixmbr.exe - Repairs the master boot record of the boot disk. The fixmbr command is only available when you are using the Recovery Console. Example: "fixmbr \Device\HardDisk0"
- Bootrec.exe tool in the Windows Recovery Environment to troubleshoot and repair startup issues in Windows Vista. The /FixMbr option writes a Windows Vista-compatible MBR to the system partition. This option does not overwrite the existing partition table. Use this option when you must resolve MBR corruption issues, or when you have to remove non-standard code from the MBR.
- MbrFix.exe - Free tool that performs several Master Boot Record (MBR) tasks like backup, restore, rewrite (fix) the boot code in the MBR, etc. Supports Windows NT, Windows 2000, Windows XP, Windows Server 2003, Windows Vista and Windows PE. Both 32-bit and 64-bit x64 edition. Don't use for GUID Partition Table (GPT) disks. Example: "MbrFix /drive 0 fixmbr /vista /yes"
- TestDisk is a powerful free data recovery softwar designed to help recover lost partitions and/or make non-booting disks bootable again.
- GAG is an open source graphical boot manager which supports multiple operating systems. The floppy or CD can be used to boot Windows (or any other OS), then use recover tools to recover the MBR.
dd if=/dev/YOURDISKHERE of=mymbr bs=446 count=1
Will perform a backup copy that can be later restored using dd :-).
What about Linux or other operating systems? Well, you're probably using GRUB or LiLO, so you can simply boot your partition using (any) LiveCD (or GAG) and restore them. As simple as boot, fsck, mount, chroot, grub - you're set. You can also try using SuperGrubBootDisk.
Posted by
cmihai
at
4:17 PM
0
comments
![]()
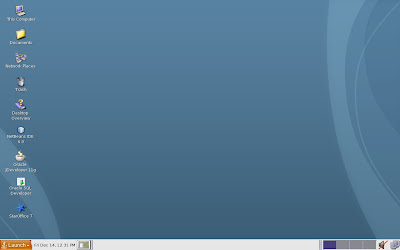
My very own DEC minicomputer - sort of
SIMH is a highly portable, multi-system simulator maintained by Bob Supnik, former DEC engineer and vice president. SIMH runs on pretty much anything: UNIX, BSD, Linux, Windows and even OpenVMS. If you're into historic computing, simulation of historic hardware or trying to migrate some really ancient applications, look into SIMH.
You can even run modern operating systems on SIMH - like OpenBSD/vax.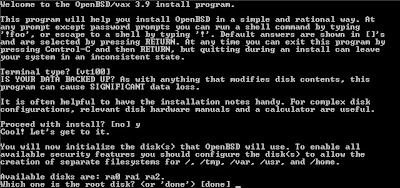
SIMH implements simulators for:
- Data General Nova, Eclipse
- Digital Equipment Corporation PDP-1, PDP-4, PDP-7, PDP-8, PDP-9, PDP-10, PDP-11, PDP-15, VAX
- GRI Corporation GRI-909
- IBM 1401, 1620, 1130, 7090/7094, System 3
- Interdata (Perkin-Elmer) 16b and 32b systems
- Hewlett-Packard 2114, 2115, 2116, 2100, 21MX
- Honeywell H316/H516
- MITS Altair 8800, with both 8080 and Z80
- Royal-Mcbee LGP-30, LGP-21
- Scientific Data Systems SDS 940
Posted by
cmihai
at
2:21 PM
0
comments
![]()
Labels: Enterprise, Mainframe, Open Source, Virtualization
Saturday, December 08, 2007
MIT OpenCourseWare - Free MIT Courses for Everyone - Berkeley too
Ever wanted to know what they teach at MIT? Well, here's your chance :-). Grab the courses and seminars, and find out!
MIT OpenCourseWare is an online repository of undergraduate and graduate-level courses from the Massachusetts Institute of Technology (MIT) available free and open to anyone, anywhere! There's about 1800 courses to go through, from Japanese Language courses to Computer Science videos and seminars :-).
So, what about the other guys, UCB? Well, this is your lucky day, because The University of California, Berkeley hosts courses on YouTube!
Posted by
cmihai
at
12:08 AM
0
comments
![]()
Labels: Documentation, Internet
Friday, December 07, 2007
Phishing for secrets
Number one reason to train your staff, deploy Intrusion Detection System, Proxy Filtering, SPAM Filtering, Antivirus, Firewall and phishing filters on your networks:
Oak Ridge National Laboratory and Los Alamos National Laboratories ("Los Alamos National Laboratory helps to ensure the safety of the nuclear weapons stockpile and reduce the threat of terrorist attacks on our homeland." [SIC]) breached via phishing attacks, unclassified material stolen.
Posted by
cmihai
at
11:58 PM
0
comments
![]()
Labels: Digital Forensics, Internet, Security
Thursday, December 06, 2007
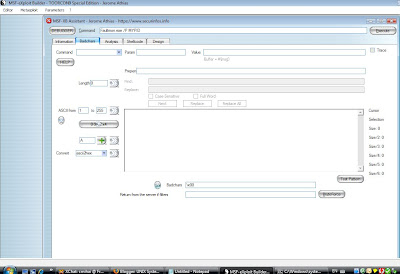
Exploit development frameworks and platforms - Metasploit, MSF-XB
Metasploit:
The Metasploit Project is an open source computer security project aids penetration testing activities and IDS signature development and provides information on security vulnerabilities.
Components:
- The Metasploit Framework is a development platform for creating security tools and exploits. The framework is used by network security professionals to perform penetration tests, system administrators to verify patch installations, product vendors to perform regression testing, and security researchers world-wide. The framework is written in the Ruby programming language (rewritten from Perl) and includes components written in C and ASM. The Metasploit Framework consists of tools, libraries, modules, and user interfaces. The basic function of the framework is a module launcher, allowing the user to configure an exploit module and launch it at a target system. If the exploit succeeds, the payload is executed on the target and the user is provided with a shell to interact with the payload.
- The Shellcode Archive contains various payloads written by the Metasploit staff. Has Windows Shellcode Development Kit.
- The Opcode Database contains the position of certain machine language opcodes in the attacked program or included DLLs
MSF-eXploit Builder
- MSF-eXploit Builder (MSF-XB) is free Windows GUI and Exploit Development PlatformMetasploit Framework exploit modules. It will help you to edit/modify/create/test exploit modules for the Metasploit Framework. It also contains an assortment of Fuzzers (TAOF, ProxyFuzz, FileFuzz, WinFuzz) and various other tools (Branchseeker, Faultmon, mycrc, nc, Findjmp2 and even pstools). It requires an installed Metasploit framework and a debugger (try Immunity Debugger).
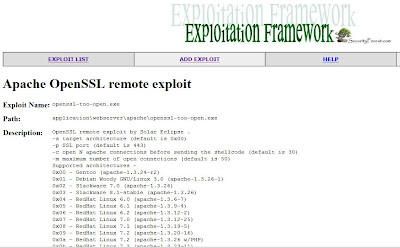
SecurityForest Exploitation Framework:
- SecurityForest's Exploitation Framework is similar in concept to Metasploit, and is written in Perl. The major difference is that it leverages the massive amount of exploits available in the ExploitTree. These exploits are publically available and do not have to be re-written to be used in the framework (no matter what language and sometimes no matter what OS). It basically acts as a Graphical User Interface to the ExploitTree which is dynamically updated at the same time as the ExploitTree.
E-mail exploitation frameworks:
- PIRANA is an exploitation framework that tests the security of a E-mail content filter. By means of a vulnerability database, the content filter to be tested will be bombarded by various emails containing a malicious payload intended to compromise the computing platform. PIRANA's goal is to test whether or not any vulnerability exists on the content filtering platform. This tool uses the shellcode generator from the Metasploit framework!
Browser Exploitation Framework:
- BeEF is the browser exploitation framework used to demonstrate the real-time impact of XSS browser vulnerabilities. Download here.
- Nikto is an Open Source web server scanner which performs comprehensive tests against web servers for multiple items, including over 3500 potentially dangerous files/CGIs, versions on over 900 servers, and version specific problems on over 250 servers. Scan items and plugins are frequently updated and can be automatically updated (if desired).
Network Vulnerability Scanners
- Nessus is a comprehensive vulnerability scanning program. Its goal is to detect potential or confirmed weaknesses on the tested machines.
- FwTest is a firewall testing tool.
Online vulnerability databases:
Posted by
cmihai
at
3:05 PM
0
comments
![]()
Labels: Debugging, Digital Forensics, Malware analysis, Security, Software Development
Immunity Debugger - an exploit development debugger
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility. It is similar to OllyDbg in functionality and interface.
Immunity Debugger is said to cut exploit development times in half and has a powerful scripting language and connectivity to fuzzers and exploit development tools.
Posted by
cmihai
at
10:12 AM
0
comments
![]()
Labels: Debugging, Digital Forensics, Malware analysis, Security, Software Development
Wednesday, December 05, 2007
Solaris podcast covers P2V migration using Etude
It covers an interesting part of Project Etude, the Solaris 8 Migration Assistant that lets you migrate legacy environments using P2V (physical-to-virtual) technologies.
Details here. Transcript here.
Posted by
cmihai
at
12:51 PM
0
comments
![]()
Labels: Enterprise, Solaris, Sun, Virtualization
Mapping a FTP/sFTP site as a drive in Windows
Mapping a FTP drive in Windows:
- Add the IP to the LMHOSTS file (it's in %systemroot%\system32\drivers\etc)
- Purge the name table cache: nbtstat -R
- net view \\YOURSITE
- net use * \\YOURSITE /user:ftp
That's it :-).
Lazy? Try fDrive, it does this for you.
Need WebDav support also? Try Novell NetDrive - you can map FTP and WebDav as drives from Windows.
Paranoid? Try sFTPDrive - you can map your files via SSH (kind of like SSHFS via FUSE on Linux/BSD).
Don't want to map, just use? Try WinSCP - a cool SCP/SFTP/FTP client for Windows.
What about NFS? Try Microsoft SUA / SFU (Services for UNIX). It's integrated just like SMB.
Posted by
cmihai
at
12:34 PM
0
comments
![]()
Labels: Microsoft, Networking
Tuesday, December 04, 2007
Sun Cluster Geographic Edition now Open Source
Sun Cluster Geographic Edition went Open Source. More data available at OpenSolaris HA Clusters community.
Download available here.
The majority of Open High Availability Cluster code is released under the Common Development and Distribution License (CDDL) Version 1.0.
Posted by
cmihai
at
11:29 PM
0
comments
![]()
Labels: Clustering, Open Source, Solaris, Sun
Codeplex - Microsofts open source project hosting website
More OpenSource from Microsoft: CodePlex is an Open Source Community Project Hosting website from Microsoft that is very much like SourceForge. So far, it has around 2500 projects. It's also got that whole Web 2.0, RSS and tag thing going on too :-).
Posted by
cmihai
at
8:51 PM
0
comments
![]()
Labels: Microsoft, Open Source, Software Development
SANS TOP-20 Security Risks for 2007
SANS Institute TOP-20 Security Risks - 2007 Annual Update
We have seen significant growth in the number of client-side vulnerabilities, including vulnerabilities in browsers, in office software, in media players and in other desktop applications. These vulnerabilities are being discovered on multiple operating systems and are being massively exploited in the wild, often to drive recruitment for botnets.
Executive summary:
"Web application vulnerabilities in open-source as well as custom-built applications account for almost half the total number of vulnerabilities being discovered in the past year."
Posted by
cmihai
at
7:57 AM
0
comments
![]()
Labels: Internet, Malware analysis, Networking, Open Source, Security
Monday, December 03, 2007
Cracking wireless keyboards
Cracking the encryption on wireless keyboards and setting up a keylogger is trivial.
Posted by
cmihai
at
9:38 AM
0
comments
![]()
Labels: BOFH, Cryptology, Security
Sunday, December 02, 2007
Internet Explorer and Firefox Vulnerability Analysis
Jeffrey Jones has published a reather interesting internet browser Vulnerability Analysis of Internet Explorer and Firefox using cross-checked references of common security bulletings such as Microsoft's Security Bulletin page, Mozilla's security announcements as well as NIST, Secunia, SecurityFocus, and many others.
The report does not cover a vulnerability Window of Exposure, or a statistic of exploits "in the wild" but it's still interesting. In a previous Internet Security Threat Report, IE had an average Window of Exposure of 9 days, followed by Safari with 5, Opera with 2 and Mozilla with 1, according to a Symantec Internet Threat Security Report.

Here's an interesting blog response from Mike Shaver.
Common Vulnerabilities and Exposures (CVE) List:
Firefox
CVE-2007-0776, CVE-2007-0777, CVE-2007-0779, CVE-2007-0981, CVE-2007-1092, CVE-2007-2292, CVE-2007-2867, CVE-2007-3734, CVE-2007-3735, CVE-2007-3737, CVE-2007-3738, CVE-2007-3845, CVE-2007-4841, CVE-2007-5338
Internet Explorer
CVE-2006-4697, CVE-2007-0024, CVE-2007-0217, CVE-2007-0218, CVE-2007-0219, CVE-2007-0942, CVE-2007-0944, CVE-2007-0945, CVE-2007-0946, CVE-2007-0947, CVE-2007-1749, CVE-2007-1750, CVE-2007-1751, CVE-2007-2216, CVE-2007-2221, CVE-2007-2222, CVE-2007-3027, CVE-2007-3041, CVE-2007-3826, CVE-2007-3892, CVE-2007-3896
Comparison of Opera, IE, Safari and Firefox
Posted by
cmihai
at
1:30 PM
0
comments
![]()
Labels: Internet, Microsoft, Open Source, Security


