The crytographic hash function MD5 has been broken. In March 2005, Xiaoyun Wang and Hongbo Yu of Shandong University in China published an article in which they describe an algorithm that can find two different sequences of 128 bytes with the same MD5 hash.
More links can also be found on Wikipedia's MD5 page.
SHA-0 has also been broken and The security of SHA-1 has been somewhat compromised by cryptography researchers. Chinese cryptographers showed that SHA-1 is not collision-free. That is, they developed an algorithm for finding collisions faster than brute force. There was also an attack reported in RIPEMD.
Practical applications of md5 collisions:
- Magnus Daum and Stefan Lucks have created two PostScript files with identical MD5 hash, of which one is a letter of recommendation, and the other is a security clearance.
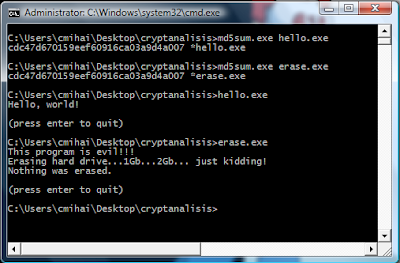
- Eduardo Diaz has described a scheme by which two programs could be packed into two archives with identical MD5 hash. A special "extractor" program turn one archive into a "good" program and the other into an "evil" one.
- Here's a pair of valid X.509 certificates that have identical signatures. The hash function used is MD5.
- Here's a paper demonstrating a technique for finding MD5 collisions quickly: eight hours on 1.6 GHz computer.
- Hashclash - Vulnerability of software integrity and code signing applications to chosen-prefix collisions for MD5
- The Status of MD5 after a recent attack (1996 whitepaper)
- Windows version:
- Linux version (i386):
What does this mean? You should use at least 2 hashing algorithms (RIPEMD-160, Tiger, WHIRLPOOL, SHA-256, SHA-512), as the chances of finding the same collisions in more than 1 hashing algorithm are practically 0.


5 comments:
md5 is getting a serious beating as time passes. There are a number of hash repositories that can get you the phrase that produces a given hash. Computers are producing via bruteforce more and more phrases.
This is useful when trying to find passwords from a given md5 hash. There are a lot of auth systems that still use just plain md5 to authenticate the user.
Bellow you can find three useful links:
http://www.md5oogle.com
http://gdataonline.com/
http://md5.rednoize.com/
The last one also has an SHA1 repository.
Have fun and don't use such services for evil!
It has already been hacked http://www.win.tue.nl/hashclash/Nostradamus/. These guys created 12 PDF files with same MD5.
I recommend using SHA1 (or better).
2 More Cosu:
http://md5.thekaine.de/
http://milw0rm.com/cracker/info.php
1 more http://md5.secure.la
MD5 considered harmful today
Creating a rogue CA certificate:
http://www.win.tue.nl/hashclash/rogue-ca/
Post a Comment